AI-First. Every Signal.
One Investigation.
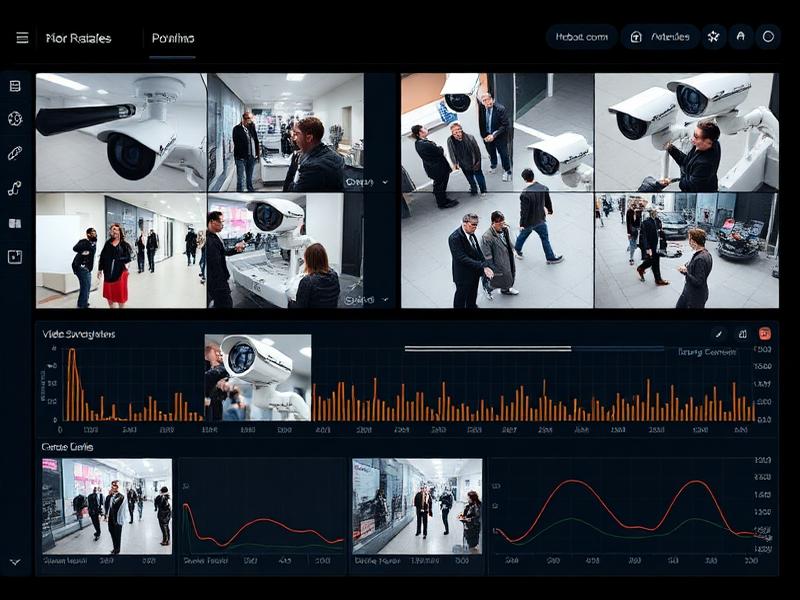
SHIELD is an AI-native intelligence fusion platform that unifies facial recognition, voice ID, telecom data, vehicle records, OSINT, and device forensics into one investigation workspace, built for agencies that can't operate on fragmented tools.
It's not AI layered on legacy systems, AI is the core, correlating identities and evidence across all sources in real time, from first input to forensic-grade output.
Investigators Have the Data. They Lack a Way to Connect It.
Agencies don’t lack data, CCTV, phone records, voice logs, vehicle data, OSINT, and device logs are all available. The problem is fragmentation: it sits across incompatible systems and formats, forcing hours of manual cross-referencing for what should be automatically connected.
SHIELD eliminates this gap by fusing SDRs, OSINT intelligence, and identity data into one correlated investigation view, automatically, without switching platforms.
AI-Native. Not AI-Added.
SHIELD is not a legacy investigation tool with an AI layer bolted on. It is an AI-native intelligence fusion platform, where every module, every data source, and every output is designed around deep learning from the ground up.
Multi-Source Ingestion
Faces, voices, phones, vehicles, SIM records, OSINT, location, social activity, and government databases, all feeding one investigation workspace simultaneously.
AI-Native Correlation
SHIELD correlates identities, behaviors, and signals across all ingested data — SDRs linked to OSINT, IMEI history linked to face matches, location pings linked to subscriber records — automatically.
Forensic-Grade Intelligence Output
Every analysis produces confidence-scored results, entity timelines, relationship maps, and SHA-256 hashed evidence packages, ready for operational use and legal proceedings.
One AI Foundation. Every Module Draws From It Simultaneously.
SHIELD's shared infrastructure means every analysis job uses the same validated models, the same identity databases, and the same secure evidence store, compounding intelligence across investigations.
Face Embedding Database
Registered identities + blacklist, searchable across all modules
Voice Embedding Store
Speaker profiles linked to face and personal records
Vector Search Engine
High-performance cosine similarity search across millions of identity vectors in real time
AI Model Registry
Centralized versioned deep learning models for detection + embedding
Unified Evidence Store
All uploaded media, extracted frames, outputs, reports, SHA-256 hashed, access-controlled
"A face registered in the live FRS system is automatically searchable in every SHIELD module, no re-registration, no duplicate databases. AI-native architecture means intelligence compounds, not fragments."
Bring More Signals Into One Investigation View
SHIELD integrates the signal types investigators actually work with, from biometric evidence and telecom data to OSINT intelligence and government records, correlating them together, not in isolation.
Facial & Visual Evidence
Images, CCTV stills, crowd footage, multi-angle photo sets. FRS + Video modules extract identity from every frame with 5-tier confidence scoring.
Audio Intelligence
Phone recordings, field audio, interview tapes. Speaker identification, voice comparison, acoustic fingerprint tamper detection.
Telecom Records — SDR & Request Management
Subscriber Details Records (SDR) queried directly via authorized operator gateways — returns full subscriber profile, linked numbers, and account status. SHIELD also generates and manages formal CDR and IPDR requests submitted to operators, maintaining a structured, deduplicated request pipeline. CDR and IPDR analysis is handled externally.
Vehicle Intelligence (VAAHAN)
Registration number, chassis, engine, owner — cross-referenced against the national VAHAN database via authorized government API. Stolen/blacklisted flag auto-surfaced.
Location & Cell Intelligence
SIM tower geolocation, Cell ID records, Tower Dump — movement reconstruction across time without requiring device GPS. Authorization-first workflow.
LBS — Location Based Services
Determine the approximate real-world location of a target device via active cell tower connections — no GPS required. SHIELD submits LBS requests through authorized operator channels and receives the serving Cell ID, approximate coordinates, and associated IMEI. A valid authorization reference is mandatory before every request.
Open Source Intelligence (OSINT)
Truecaller lookups, online account discovery, public records, company registries, court records, and electoral rolls — aggregated into a single OSINT profile card. All data points tagged with source URL, retrieval timestamp, and confidence level for independent verification.
Device Forensics — IMEI + WhatsApp
IMEI history lookup for SIM-switching detection. WhatsApp and Facebook account data retrieved via formal legal requests to Meta through designated cybercrime authority channels — returns account registration details, device fingerprint, IP access history, and last active timestamp. Authorized formal request workflow built in.
Intelligence Databases & Alerts
CT-POI dossiers with full criminal and FIR history. POI flags (Person of Interest registry). LOC — Lookout Circulars triggering border and immigration alerts. Interpol Red, Blue, Green, Yellow, and Black Notice checks. SAANJH government records (passport, tenant, arms licence, missing persons). Field intelligence from the Suspects Module with A1–E5 intelligence grading.
Global Search
Enter any single identifier, name, phone number, vehicle plate, IMEI, IP address, case number, and SHIELD queries every connected source simultaneously, returning a ranked, cross-linked intelligence summary.
SDRs. OSINT. Identity. Location. Correlated in One View.
When subscriber records, OSINT intelligence, and identity data are analyzed together, not in separate tools, investigators see connections that would never surface in any single system.
SHIELD's unified workspace lets analysts move from any raw identifier to a complete suspect intelligence picture without switching platforms. This is what it means to be AI-native rather than AI-added.
Four Specialized Engines.
One Integrated Intelligence Platform.
Each module is purpose-built for a specific evidence type. Together, they feed the unified investigation workspace with correlated, confidence-scored, cross-linked intelligence.
From Fragmented Evidence to a Unified Intelligence Picture
Every SHIELD investigation follows a structured, auditable, legally defensible path — from evidence submission to forensic-grade output.
Evidence Ingestion
Submit images, video, audio, phone numbers, vehicle plates, IMEI numbers, case references, or location data. Every submission logged with analyst credentials — job ID assigned immediately.
Normalization & Pre-Processing
Media quality-assessed and normalized: resolution checked, audio noise reduced, frames extracted, format validated. Low-quality inputs flagged before AI processing begins.
Multi-Engine AI Analysis
Face detection + embedding, speaker diarisation + voice embedding, people tracking + unique-face clustering, composite identity generation — all running simultaneously.
Cross-Source Correlation
Results automatically cross-referenced: a face match surfaces linked phone records; a phone number surfaces vehicle registrations, location history, SDR subscriber profile, OSINT intelligence, and Suspects module entries — through the Global Search correlation layer.
Analyst Review & Scoring
Ranked results with 5-tier confidence bands surfaced for human review. Blacklist matches receive CRITICAL priority. Analysts validate, merge, flag, or escalate findings.
Export & Case Documentation
Investigation reports auto-generated — PDF, CSV, JSON. Evidence hashed (SHA-256) at export. Full audit trail: every search, access, and export immutably logged.
Moving From Reactive Investigation to Predictive Intelligence
SHIELD is built not just to solve cases after incidents, but to identify suspicious patterns, recurring signals, and early-warning indicators before they escalate.


Identify recurring suspects, locations, vehicles, or communication patterns across multiple investigations, surfaced automatically without manual cross-case comparison.
Detect unusual changes — movement shifts, contact frequency spikes, new device associations, new social account activity — that may indicate escalating threat activity.
Use prior case intelligence to flag individuals or networks matching emerging suspicious profiles, identifying potential threats before a formal investigation is opened.
Predictive intelligence capabilities are part of SHIELD's forward development roadmap. Current platform delivers full post-event forensic intelligence with operational deployment readiness.
Built for Real Investigations. Not Demo Conditions.
Every design decision in SHIELD reflects how investigators actually work, with imperfect evidence, fragmented sources, and no room for black-box decisions.
AI-Native, Not AI-Added
SHIELD was designed around AI from the ground up. Every module, every data correlation, and every output is AI-native — not a legacy tool with machine learning bolted on.
15+ Source Types in One Workspace
SDRs, OSINT, biometrics, government records, device logs — all correlated in one interface. Not one tool per source type.
Ranked Evidence, Not Binary Verdicts
Every match returns a confidence band from Definitive (95–100%) to No Match. Analysts review scored evidence — the platform never makes the call for them.
Intelligence That Compounds Across Sources
A phone number search surfaces linked vehicles, OSINT profiles, cell history, face match records, and prior SHIELD job appearances — automatically, through Global Search.
Forensic-Grade Evidence Integrity
SHA-256 hashing at ingestion. AES-256 encryption at rest. TLS 1.3 in transit. Immutable audit trail per job. Every output includes a verifiable chain-of-custody log — built for investigations that require evidence integrity at every step.
Calibrated for Operational Reality
Audio pre-processing for noisy recordings. Partial face support. Low-light image enhancement. Telephony-grade voice matching. Built for field evidence, not lab conditions.
Controlled Access. Evidence Integrity. Full Auditability.
SHIELD processes biometric, telecom, and personal data classified as Special Category. Every control is built for investigative and legal requirements.
Enterprise-Grade Security
Every layer — storage, transit, access, audit — built for agencies handling classified evidence.
AES-256 Encryption at Rest
AES-256All uploaded media, extracted embeddings, and generated reports encrypted at rest. No unencrypted evidence data at any storage layer.
TLS 1.3 Encryption in Transit
TLS 1.3All client-server-storage transfers secured with TLS 1.3. Evidence never transmitted over unencrypted channels.
SHA-256 Evidence Hashing
SHA-256Every uploaded file is cryptographically hashed at ingestion. Any post-upload modification is detectable, supporting evidence integrity requirements for investigations that require a verifiable chain of custody.
Immutable Audit Trail
100%Every job submission, result access, database query, and export logged with user ID, IP address, and timestamp. Unalterable. Compliance-ready.
Role-Based Access Control
3-TierAdmin (full access), Agent (submit + review + export), Viewer (read-only). Each organization in a fully isolated multi-tenant data partition.
Configurable Retention
FlexibleTenant-controlled retention periods aligned to jurisdiction-specific compliance requirements, 90 days, 12 months, or indefinite.
Built for High-Stakes Investigation Environments
SHIELD is deployed where agencies need faster identification, deeper intelligence, and evidence that holds up to legal scrutiny.
Intelligence Platform Built for Operational Deployment
Global Search queries 10+ connected data sources from a single identifier, name, number, plate, IMEI, or IP.
SHIELD generates and manages formal CDR, IPDR, and Tower Dump requests to telecom operators, with built-in deduplication to prevent duplicate requests and a full audit trail per submission.
Multi-Image composite identity achieves up to 98% match accuracy under ideal conditions; 83–87% under challenging field evidence scenarios.
See How SHIELD Correlates Your Evidence Into Actionable Intelligence
Whether for post-incident investigation, case development, or multi-source suspect identification, the next step is a guided demo tailored to your evidence environment and workflow.